| Version 19 (modified by , 12 years ago) (diff) |
|---|
Contents
AccountManager
- Package
- acct_mgr.api
This holds core code of this plugin. This component must be enabled to use any of the other components.
Additionally one or more sources for storing authentication information are required:
- PasswordFileStores
- HttpAuthStore
- SessionStore
- SvnServePasswordStore
There's even some information on how to get not-yet-implemented LDAP authentication.
AccountManagerAdminPages note1
- Package
- acct_mgr.admin
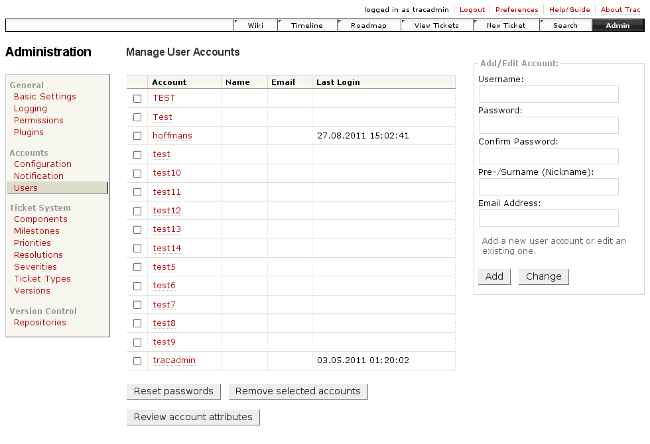
This component adds a whole new section with a couple of pages to the trac:WebAdmin section for managing user accounts:
- admin/accounts/config - basic configuration, i.e. AuthStore activation and ordering
- admin/accounts/notification - AccountManager change notification settings
- admin/accounts/users - user account listing with some management functions, i.e.
- add/delete accounts
- change password and other account attributes
- reset password similar to the 'lost password', but triggered by admin (since acct_mgr-0.3)
- review account details (since acct_mgr-0.3)
- review and erase entries of Trac db table
session_attribute(since acct_mgr-0.4) note2
note1 In version acct_mgr-0.3, module name was AccountManagerAdminPage. If you are upgrading to acct_mgr-0.4 from an earlier version, and this feature was enabled using acct_mgr.admin.AccountManagerAdminPage, this feature will now be disabled until it is enabled using acct_mgr.admin.AccountManagerAdminPages.
note2 Requires ACCTMGR_ADMIN or TRAC_ADMIN, but handle with extreme care anyway - no problem to shoot yourself in the foot by i.e. deleting your own SessionStore admin password. So double-check and think twice, and especially have a current, working Trac db backup before starting cleanup here.
Older versions required the TRAC_ADMIN permission to access any of the admin pages, but a more granular set of permissions has been introduced since acct_mgr-0.3 (see changeset [9280]):
ACCTMGR_ADMIN- all permissions in the plugin's domain, like
TRAC_ADMINfor Trac core ACCTMGR_CONFIG_ADMIN- permission to see and use the configuration admin page
ACCTMGR_USER_ADMIN- permission to see and use most other admin pages of this plugin except the cleanup (button <Review account attributes>)
Configuration
[components] acct_mgr.admin.AccountManagerAdminPages = enabled
NOTE: If you are upgrading to acct_mgr-0.4 from an earlier version, and this feature was enabled using acct_mgr.admin.AccountManagerAdminPage, this feature will now be disabled until it is enabled using acct_mgr.admin.AccountManagerAdminPages.
Compatibility
requires Trac >= 0.10
AccountModule
- Package
- acct_mgr.web_ui
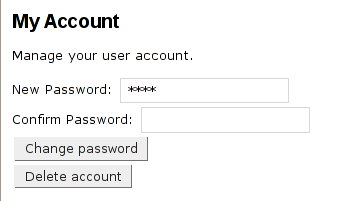
Allows users to change their password, or delete their account. When logged in it will appear as a tab “Account” after clicking the “Preferences” link.
Configuration
[components] acct_mgr.web_ui.AccountModule = enabled
You'll need to activate at least one of the authentication resources bundled with AccountManagerPlugin. (From a programmers view these are all IPasswordStore implementations.) An error telling you "This password store does not support listing users" indicates, that you didn't successfully activate/configure any authentication credential provider yet. Easiest way to do that is using the web-UI. Just go to admin/accounts/config and select a value different from setting "--" at least for one of the authentication resources listed there.
Disabling account deletion
If you want your users to be able to change their password in Trac user preferences (see 'Account' tab of 'Preferences' from the meta navigation bar), but don't want them to be able to delete their account, you should configure as follows in trac.ini (since acct_mgr-0.3):
[account-manager] allow_delete_account = false
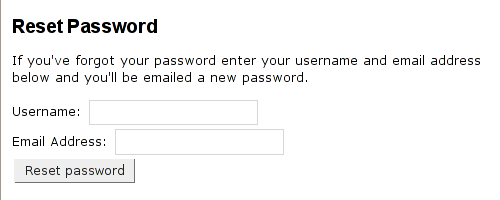
Since Trac 0.10: When used in combination with the LoginModule it adds a link to the login page “Forgot your password?” where users can reset their password if they’ve forgotten it. You will need to have your SMTP server information configured in your trac.ini for the “Forgot your password?” link to show up and enable AccountChangeListener:
[components] acct_mgr.notification.accountchangelistener = enabled
Disabling password reset
To disable just the password reset functionality add the following line to the [account-manager] section:
[account-manager] reset_password = false
Since Trac 0.11: When a user resets their password they will be required to change their password on the next successful login. This can be disabled via the trac.ini by setting:
[account-manager] force_passwd_change = false
LoginModule
- Package
- acct_mgr.web_ui
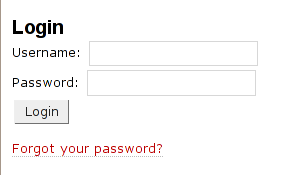
Allows users to login via a HTML form instead of using HTTP authentication.
The template has been modified for acct_mgr-0.3 to allow for better custom CSS styling. See style.css in the contrib directory for a jump-start.
Configuration
To use the AccountManager’s HTML form, you need to explicitly disable Trac's own HTTP authentication module. To do so add this your trac.ini or find and modify existing lines accordingly:
[components] acct_mgr.web_ui.LoginModule = enabled trac.web.auth.LoginModule = disabled
When using the tracd server be sure not to use the --auth or --basic-auth options. Using either of these options will cause tracd to popup the username/password dialog box and you will not be able to use AccountManagerPlugin's HTML form.
If you have previously enabled authentication for Trac on Apache, you will need to disable it or Apache will popup the username/password dialog and you will be unable to use the HTML form. In order to disable the authentication look for a section in the Apache configuration file like:
<Location /trac/login> # Some options like AuthType and AuthUserFile Require valid-user </Location>
Deleting or commenting the Require valid-user line should be sufficient to disable HTTP authentication. After you’ve tested it, you can probably delete or comment out the rest of the authentication options. In some pre-bundled packages as Bitnami Trac you will find it inside an apache configuration extension as trac.conf (BitnamiTrac\trac\conf\trac.conf)
Compatibility
requires Trac >= 0.10
To use this module with tracd stand-alone server you'll need Trac 0.10 or later version, or an external webserver such as Apache.
AccountGuard
- Package
- acct_mgr.guard
appears in acct_mgr-0.3: adds login failure tracking and administrative account locking to protect against brute-force attacks on user passwords
Enabling the guard means, that even legitimated login attempts will get rejected as long as account lock conditions are met. So an account is not reachable for the user while under attack. An admin could still log in (to a different account), check the source(s) of the malicious login attempts and stop them by other means to help the user restore access to his/her account.
See some example configurations it the cookbook page and look at screenshot series below to get an idea, how this looks like and is meant to work.
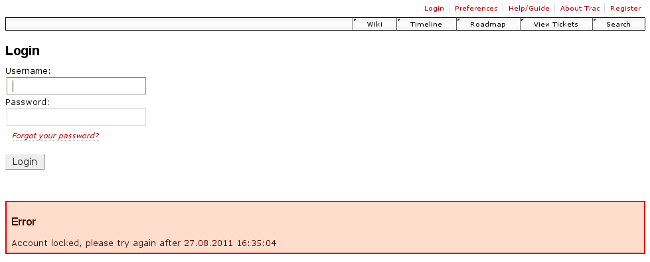
Hitting account soft (temporary) lock condition on login failure
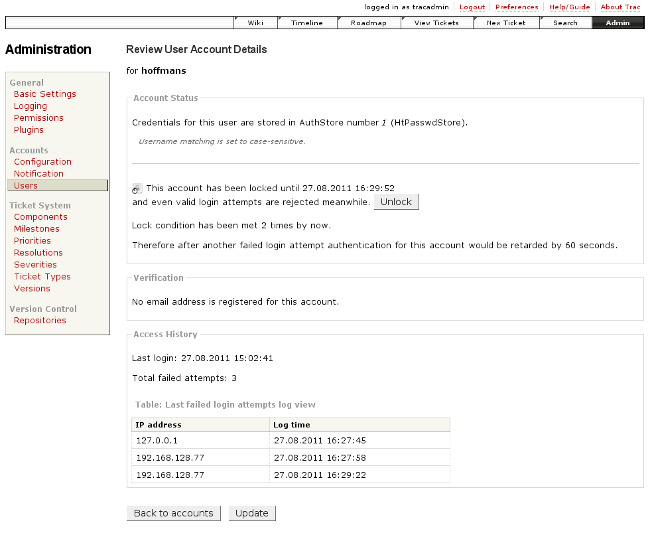
Account details page showing failed login attempts and other details
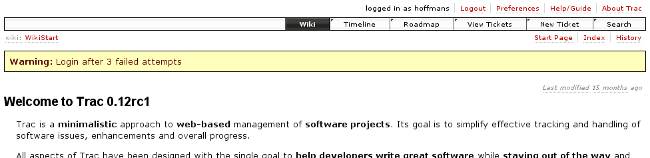
Display of total failed login attempts since last successful login
See also: AccountManagerPlugin/RegistrationInspector, CookBook/AccountManagerPluginConfiguration
Attachments (4)
-
login-form_v0.3_custom.png (6.8 KB) - added by 13 years ago.
screenshot of login form - v0.3 with custom style
-
acct_mgr-admin_acct-details_v0.3.png (84.3 KB) - added by 13 years ago.
account details admin page with failed login attempts
-
acct_mgr_with_acct-guard_login-failure_v0.3.png (18.4 KB) - added by 13 years ago.
account manager login page when hitting temporary account lock condition on login failure
-
acct_mgr_with_acct-guard_login-success_v0.3.png (35.2 KB) - added by 13 years ago.
failed login attemps display after successful login
Download all attachments as: .zip